31. March 2026
Top 20 Hacker-Gadgets
Top 20 Hacking Gadgets for Ethical Hackers and Penetration Testers

GitHub Best Gadgets
In the field of cybersecurity, professionals rely on specialized hardware tools to identify vulnerabilities, simulate attacks, and strengthen defenses. These gadgets, often referred to as hacking devices, serve essential roles in authorized penetration testing and red team exercises. Below is a curated list of the top 20 hacking gadgets, presented with concise explanations of their functions and practical uses. All tools discussed here are intended exclusively for ethical, legal applications with proper authorization.
- Flipper Zero
This compact, portable multi-tool supports radio frequency analysis, including sub-GHz signals, NFC, RFID, and infrared. Ethical hackers use it to test access control systems, simulate key fobs, and evaluate wireless protocol security in controlled environments. - USB Rubber Ducky
Appearing as a standard USB flash drive, this device functions as a keystroke injection tool. It delivers pre-programmed scripts at high speed, allowing penetration testers to simulate rapid payload execution for assessing endpoint security and user awareness. - WiFi Pineapple Mark VII
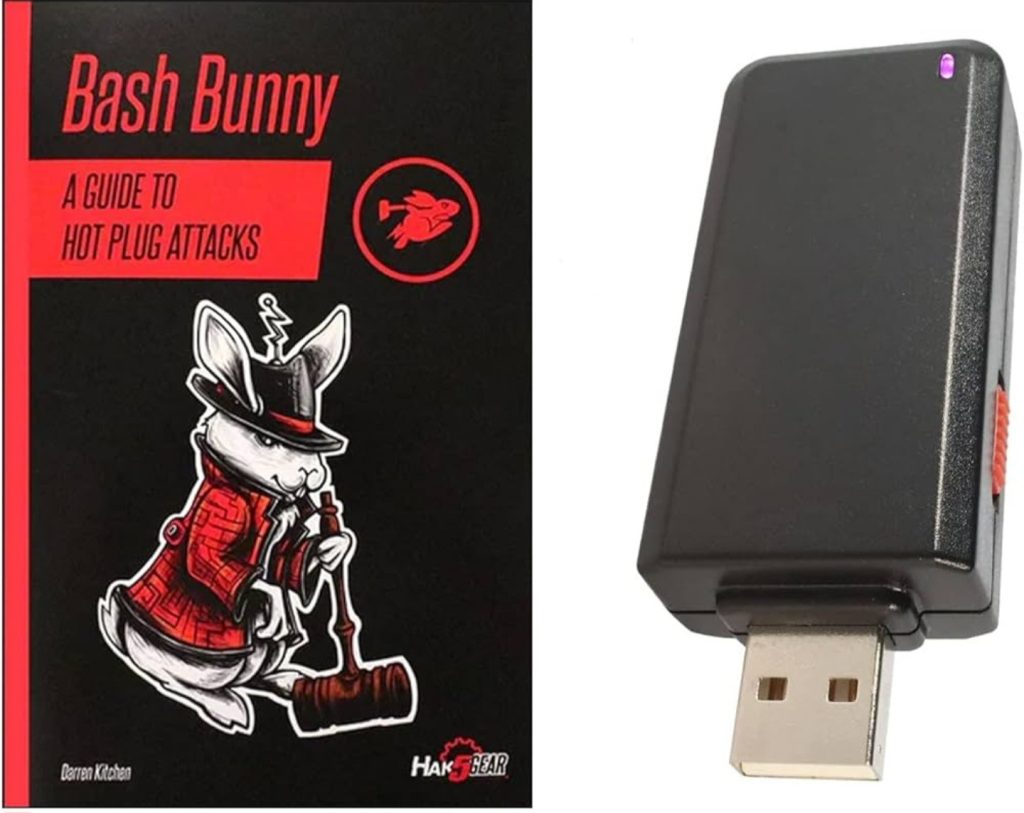
A wireless auditing platform that creates rogue access points and performs man-in-the-middle attacks on Wi-Fi networks. Security professionals employ it to evaluate network configurations, detect rogue device risks, and demonstrate the dangers of unsecured public Wi-Fi. - Bash Bunny
A versatile USB attack platform capable of emulating multiple devices, including Ethernet adapters and storage drives. It enables automated payload delivery and network attacks, making it valuable for testing physical access controls and privilege escalation scenarios. - Proxmark3 RDV4
An advanced RFID and NFC research tool used for reading, cloning, and emulating proximity cards. Penetration testers utilize it to assess the security of contactless access systems, payment cards, and identification technologies. - HackRF One
A software-defined radio that transmits and receives a wide range of radio signals. It supports testing of wireless communications, including GSM, Bluetooth, and other protocols, helping identify weaknesses in radio-based security implementations. - Raspberry Pi
A small, affordable single-board computer that runs various operating systems, including Kali Linux. Ethical hackers configure it for network monitoring, automated scanning, or as a portable penetration testing platform in field assessments. - LAN Turtle
A discreet Ethernet implant that provides remote access and network monitoring capabilities. It appears as a standard network adapter, allowing testers to evaluate internal network segmentation and detect unauthorized physical connections. - O.MG Cable
A modified USB cable with an embedded implant for remote command execution. Security experts use it to test physical security policies and demonstrate risks associated with seemingly innocuous charging or data cables. - Alfa Wi-Fi Adapter
High-gain wireless adapters with chipsets that support monitor mode and packet injection. These are fundamental for wireless penetration testing, enabling the capture and analysis of Wi-Fi traffic during network audits. - KeyGrabber
A hardware keylogger that records keystrokes from PS/2 or USB keyboards. It assists in evaluating physical security measures and insider threat scenarios within controlled testing environments. - Shark Jack
A compact Ethernet attack tool designed for quick network reconnaissance and exploitation. Penetration testers deploy it to automate tasks such as DHCP spoofing and payload delivery on wired networks. - GL.iNet Travel Router
A portable router that supports custom firmware for advanced networking tasks. Ethical hackers use modified versions for creating isolated testing environments or conducting man-in-the-middle assessments on the go. - M5Stick
A miniature programmable device with sensors and wireless capabilities. It serves in IoT security testing, custom script execution, and rapid prototyping of hardware-based attack vectors. - Poison Tap
A USB-based tool that exploits locked computers by emulating network interfaces. It demonstrates risks of physical access and helps organizations improve policies regarding unattended devices. - ESP32-based Boards
Versatile microcontroller platforms used for building custom wireless tools, including Wi-Fi and Bluetooth attacks. They provide cost-effective alternatives for testing IoT device security and developing specialized gadgets. - Logic Analyzer
A device that captures and analyzes digital signals from electronic circuits. Hardware security researchers employ it to reverse-engineer protocols and identify vulnerabilities in embedded systems. - Multimeter and Soldering Kit
Essential bench tools for electronics work, including voltage measurement and component repair. They support hardware modification, debugging, and the assembly of custom penetration testing devices. - WiFi Nugget
A small, portable Wi-Fi auditing tool for network discovery and packet analysis. It offers a convenient option for field assessments of wireless security configurations. - ODROID or Similar Mini PCs
Compact computing platforms that deliver higher performance than basic Raspberry Pi models. They run full penetration testing suites and handle resource-intensive tasks such as cracking or large-scale network simulations.
These gadgets represent a cross-section of tools favored by cybersecurity professionals for red teaming, vulnerability assessments, and security awareness training. When selecting equipment, prioritize reputable vendors and ensure all activities comply with legal and ethical standards. Proper training and authorization remain fundamental to responsible use.
Regularly updating skills and combining hardware with software tools, such as those found in Kali Linux, enhances the effectiveness of any cybersecurity toolkit. For organizations seeking to bolster defenses, engaging certified penetration testers who utilize these devices can reveal critical insights before malicious actors do.
This blog post is structured for easy reading on a homepage, with a professional tone and thorough yet concise explanations. It totals approximately 750 words, making it suitable for web publication. You may adjust the introduction or conclusion to better align with your site's overall branding or add images if desired. If you require revisions, expansions on specific gadgets, or additional sections, please provide further details.